Network topology
We provide three fulfillment options for different networking needs.
- Dedicated public VPC (recommended)
- Dedicated private VPC
- Existing VPC
When optinmizing for costs we recommend the fulfillment option Dedicated public VPC. In case running bucketAV in a public subnet is not an option due to security regulations, use the fulfillment option Dedicated private VPC but expect baseline AWS costs of about $200/month for networking. The third option gives you full control over the network configuration: the fulfillment option Existing VPC. But, deploying to an existing VPCs comes with two downsides. First, in our opinion, you should isolate the network used by bucketAV to scan potentially infected files from any other networks. Second, the complexity of setting up bucketAV increases when choosing the fulfillment option Existing VPC.
Dedicated public VPC
VPC is managed by bucketAV. Scan Fleet runs in public subnets.
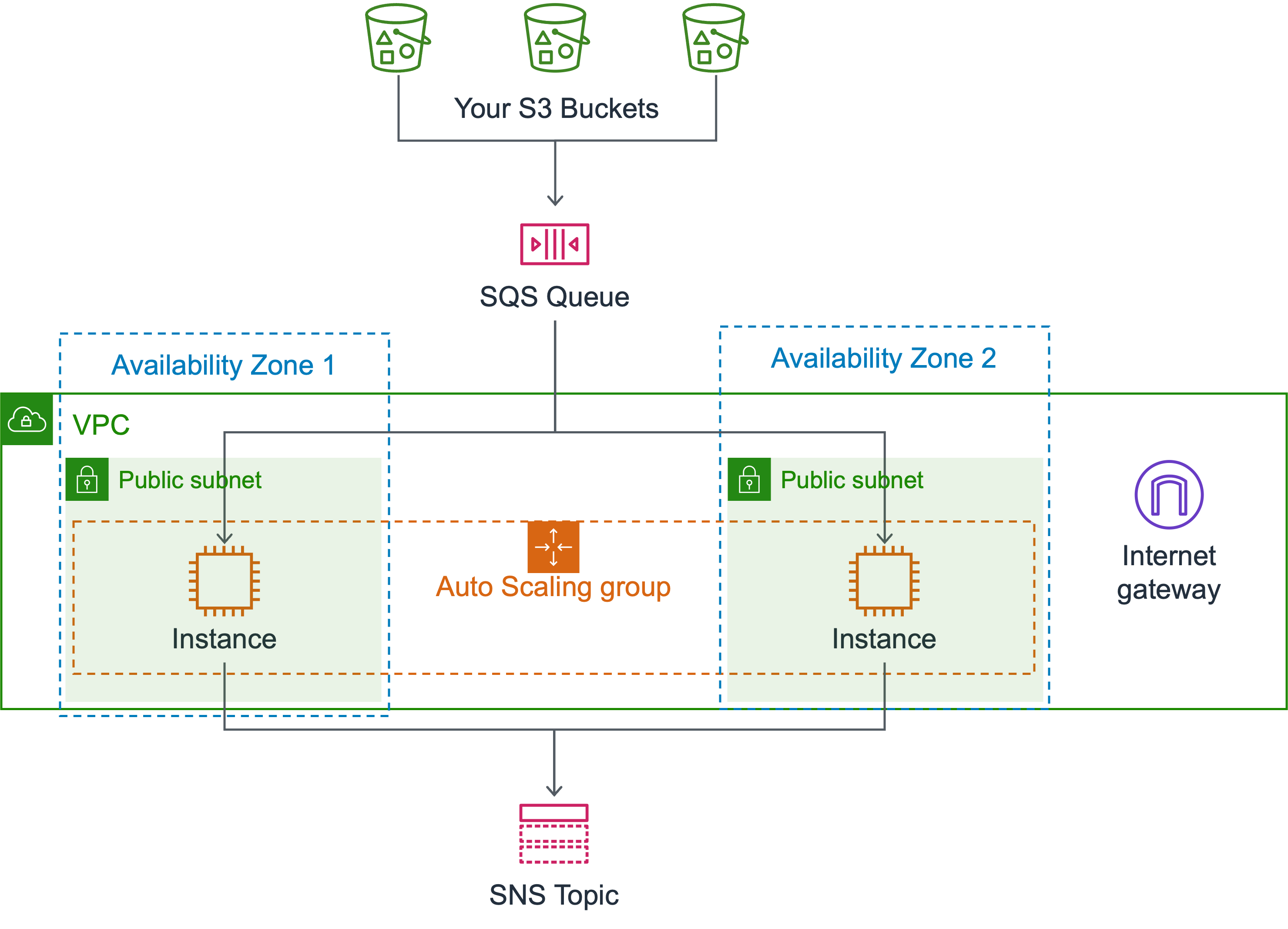
- VPC
- CIDR
10.0.0.0/16configurable via the VpcCidrBlock configuration parameter and VpcSubnetCidrBits configuration parameter. - Flow Logs turned on.
- Internet Gateway
- CIDR
- Two public subnets
- NACLs allow inbound port 22 (SSH) restricted to CIDR defined in the SSHIngressCidrIp configuration parameter and high ports.
- NACLs allow outbound port 443 (AWS API, virus database, Amazon Linux 2023 repository), and high ports.
- Public IP address
- Security group
- Allow inbound port 22 restricted to CIDR defined in the SSHIngressCidrIp configuration parameter.
- Allow outbound port 443.
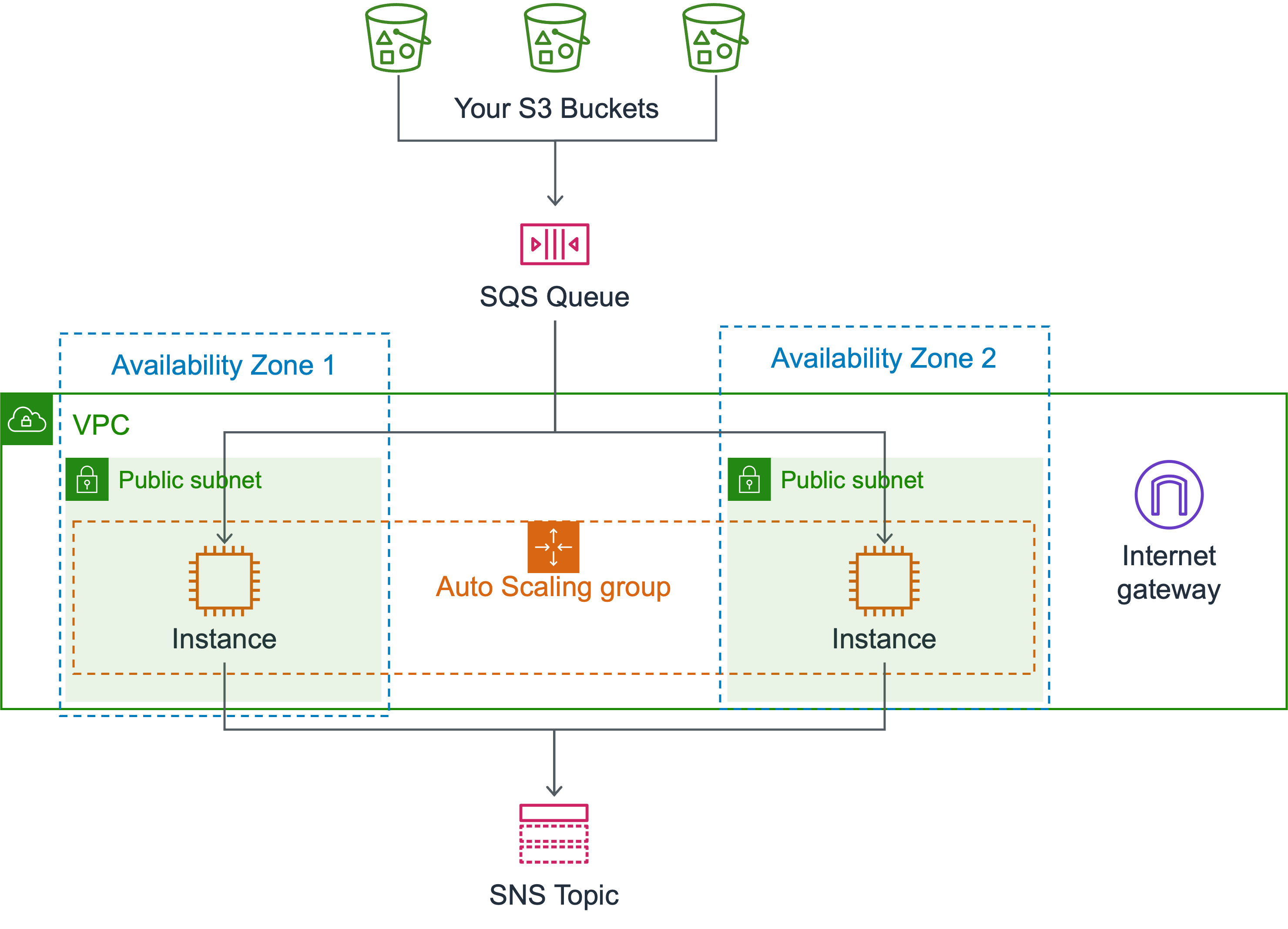
- VPC
- CIDR
10.0.0.0/16configurable via the VpcCidrBlock configuration parameter and VpcSubnetCidrBits configuration parameter. - Flow Logs turned on.
- Internet Gateway
- CIDR
- Two public subnets
- NACLs allow inbound port 22 (SSH) restricted to CIDR defined in the SSHIngressCidrIp configuration parameter and high ports.
- NACLs allow outbound port 443 (AWS API, virus database, Amazon Linux 2023 repository), and high ports restricted to CIDR defined in the SSHIngressCidrIp configuration parameter.
- Public IP address
- Security group
- Allow inbound port 22 restricted to CIDR defined in the SSHIngressCidrIp configuration parameter.
- Allow outbound port 443.
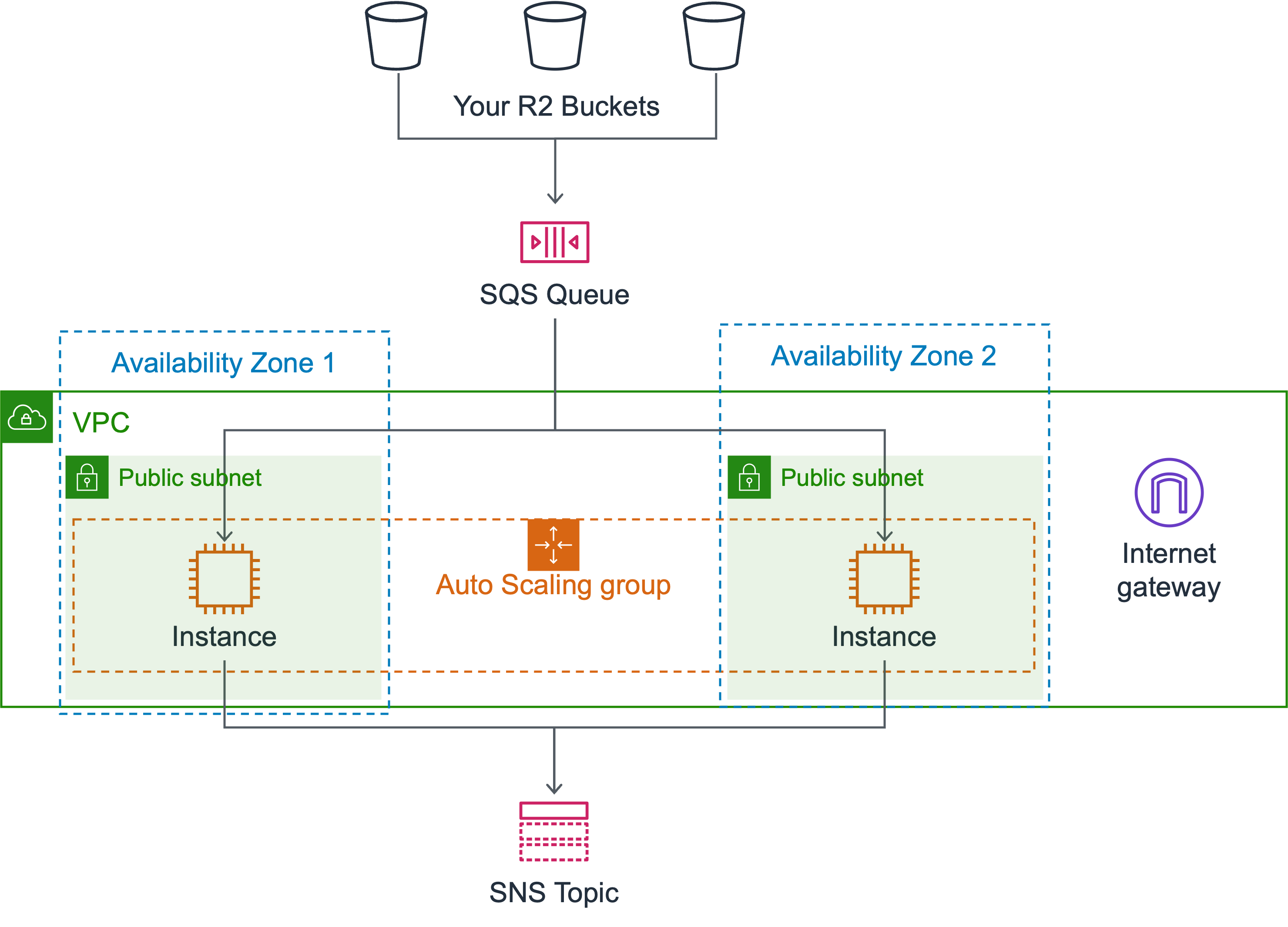
- VPC
- CIDR
10.0.0.0/16configurable via the VpcCidrBlock configuration parameter and VpcSubnetCidrBits configuration parameter. - Flow Logs turned on.
- Internet Gateway
- CIDR
- Two public subnets
- NACLs allow inbound port 22 (SSH) restricted to CIDR defined in the SSHIngressCidrIp configuration parameter and high ports.
- NACLs allow outbound port 443 (AWS API, virus database, Amazon Linux 2023 repository), and high ports restricted to CIDR defined in the SSHIngressCidrIp configuration parameter and high ports.
- Public IP address
- Security group
- Allow inbound port 22 restricted to CIDR defined in the SSHIngressCidrIp configuration parameter.
- Allow outbound port 443.
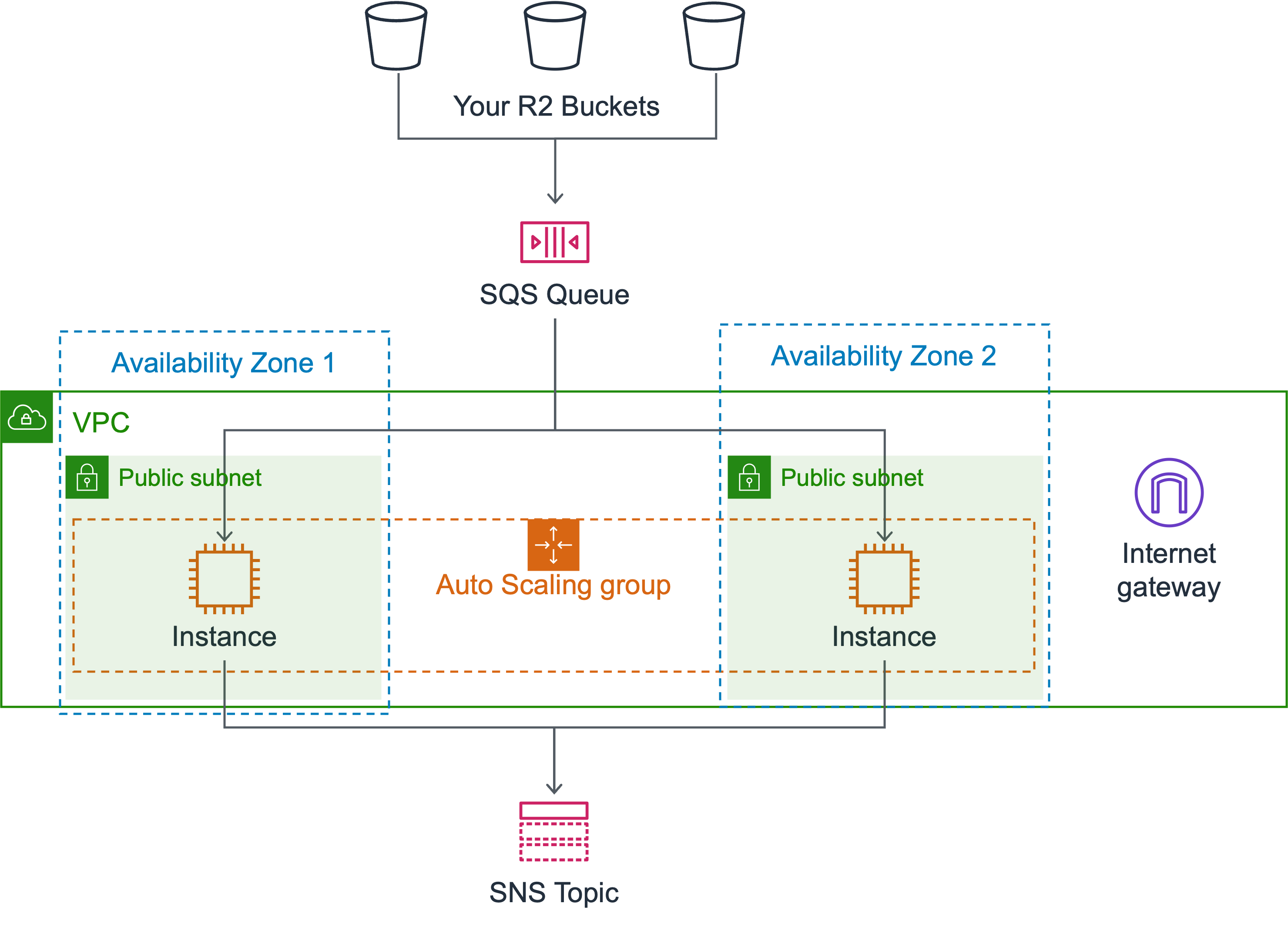
- VPC
- CIDR
10.0.0.0/16configurable via the VpcCidrBlock configuration parameter and VpcSubnetCidrBits configuration parameter. - Flow Logs turned on.
- Internet Gateway
- CIDR
- Two public subnets
- NACLs allow inbound port 22 (SSH) restricted to CIDR defined in the SSHIngressCidrIp configuration parameter and high ports.
- NACLs allow outbound port 443 (AWS API, virus database, Amazon Linux 2023 repository), and high ports restricted to CIDR defined in the SSHIngressCidrIp configuration parameter and high ports.
- Public IP address
- Security group
- Allow inbound port 22 restricted to CIDR defined in the SSHIngressCidrIp configuration parameter.
- Allow outbound port 443.
Dedicated private VPC
VPC is managed by bucketAV. Scan Fleet runs in private subnets.
Expect costs of about $14.60/month per VPC interface endpoint plus $0.01/GB traffic!
- VPC
- CIDR
10.0.0.0/16configurable via the VpcCidrBlock configuration parameter and VpcSubnetCidrBits configuration parameter. - Flow Logs turned on.
- CIDR
- Two private subnets
- NACLs allow inbound port 443 required by VPC interface endpoints, port 22 (SSH) restricted to CIDR defined in the SSHIngressCidrIp configuration parameter, as well as high ports required by VPC gateway & interface endpoints.
- NACLs allow outbound port 443, as well as high ports restricted required by VPC gateway & interface endpoints
- Gateway VPC Endpoints for DynamoDB and S3.
- Interface VPC Endpoints forSNS, EventBridge, SQS, EC2 Auto Scaling, STS, CloudFormation, CloudWatch, CloudWatch Logs, SSM, Secrets Manager, Markerplace, API Gateway;
- Security group
- Allow inbound port 22 restricted to CIDR defined in the SSHIngressCidrIp configuration parameter.
- Allow outbound port 443 to VPC interface endpoints, port 443 to DynamoDB and S3 APIs.
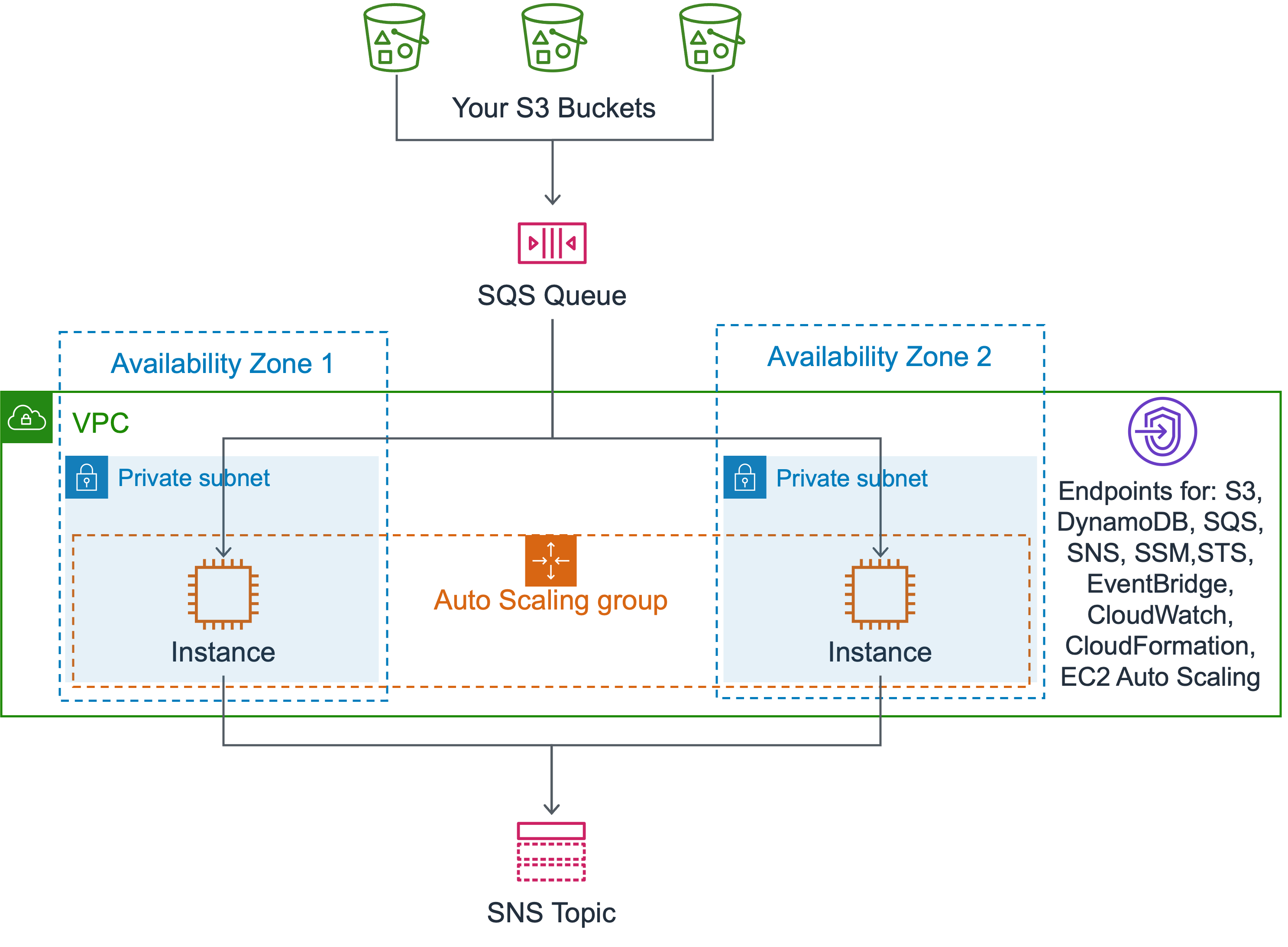
Expect costs of about $14.60/month per VPC interface endpoint plus $0.01/GB traffic!
- VPC
- CIDR
10.0.0.0/16configurable via the VpcCidrBlock configuration parameter and VpcSubnetCidrBits configuration parameter. - Flow Logs turned on.
- CIDR
- Two private subnets
- NACLs allow inbound port 443 required by VPC interface endpoints, port 22 (SSH) restricted to CIDR defined in the SSHIngressCidrIp configuration parameter, as well as high ports required by VPC gateway & interface endpoints.
- NACLs allow outbound port 443, as well as high ports restricted required by VPC gateway & interface endpoints
- Gateway VPC Endpoints for DynamoDB and S3.
- Interface VPC Endpoints for SNS, EventBridge, SQS, EC2 Auto Scaling, STS, CloudFormation, CloudWatch, CloudWatch Logs, SSM, Secrets Manager;
- Security group
- Allow inbound port 22 restricted to CIDR defined in the SSHIngressCidrIp configuration parameter.
- Allow outbound port 443 to VPC interface endpoints, port 443 to DynamoDB and S3 APIs.
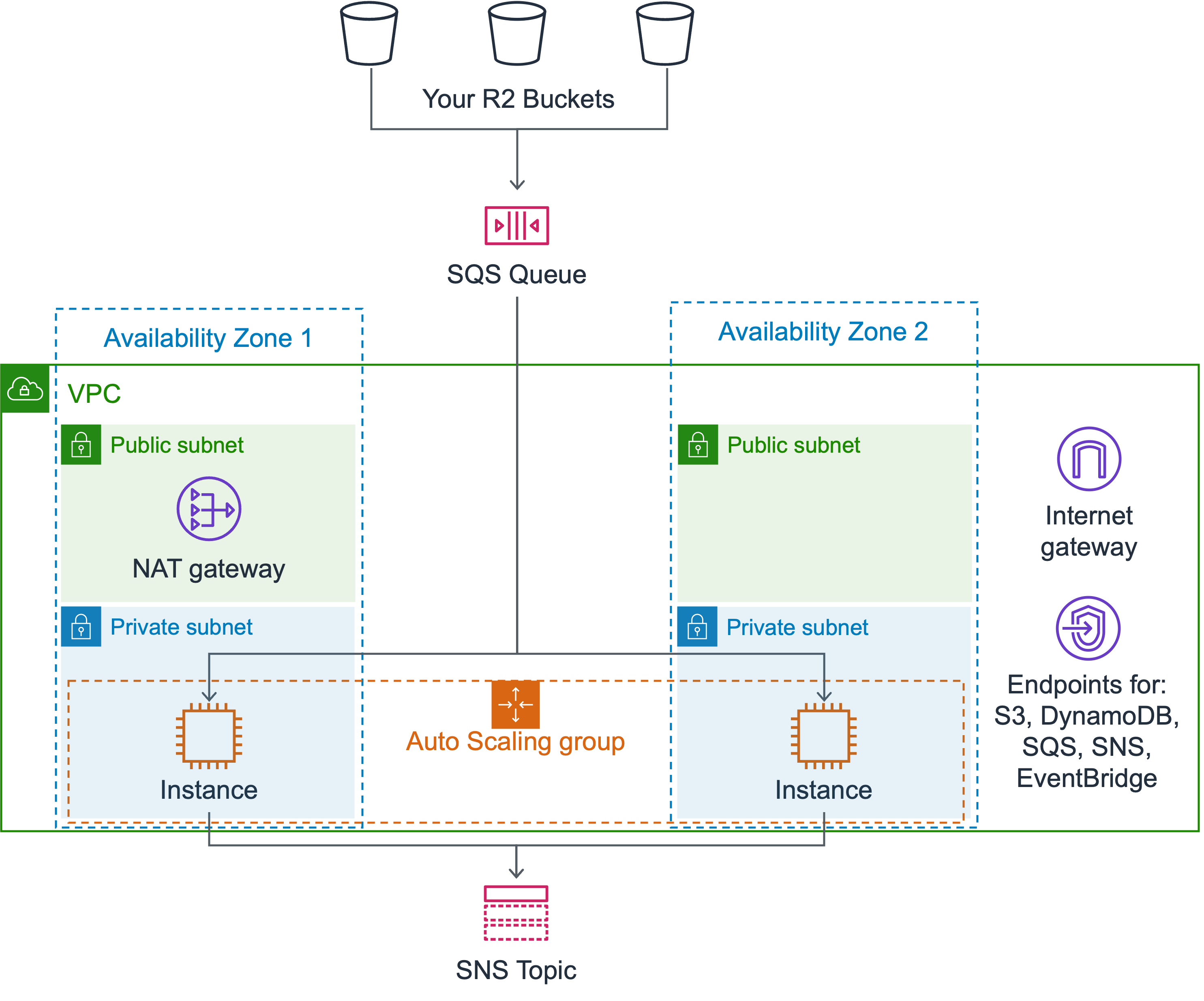
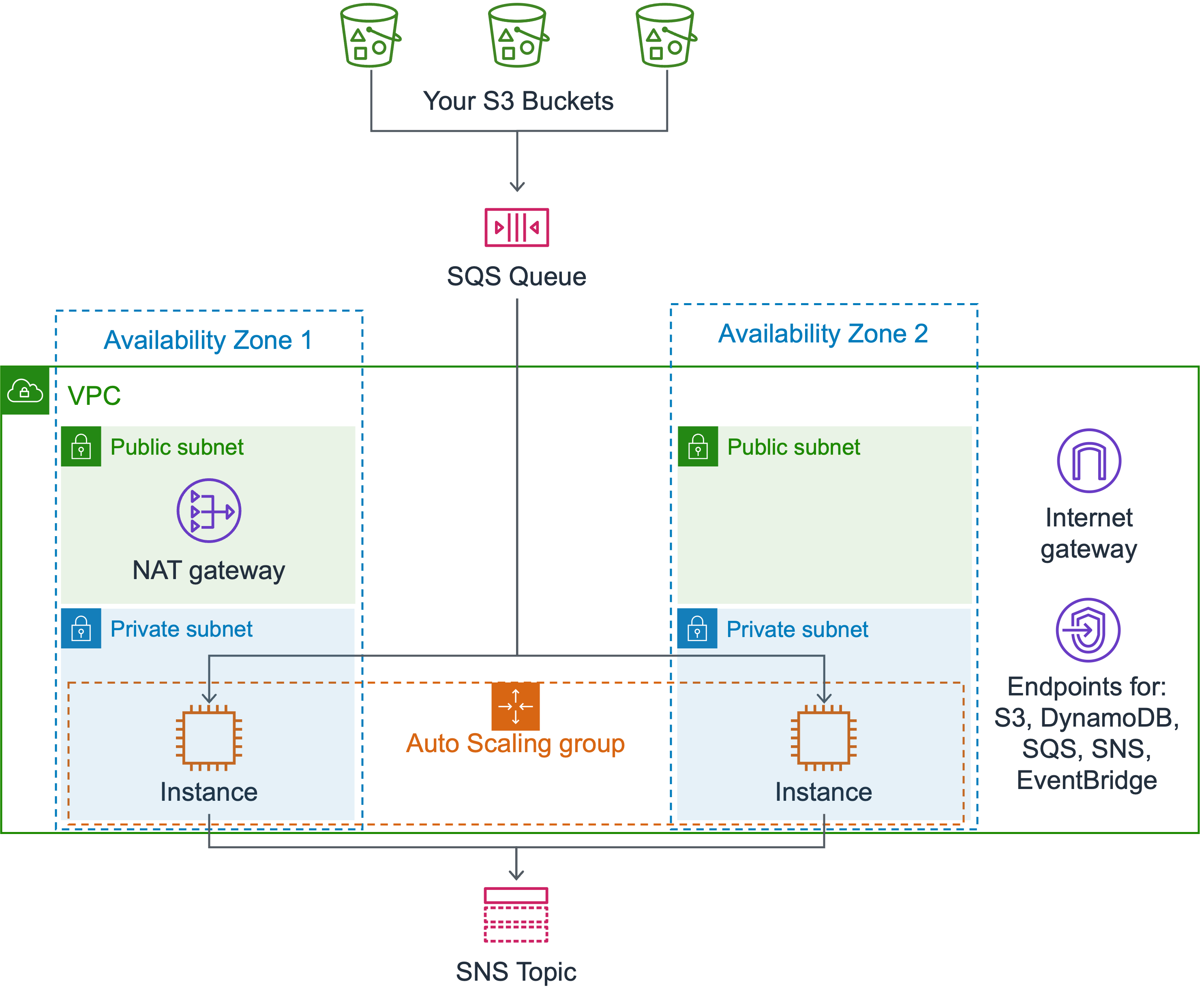
Expect costs of about $14.60/month per VPC interface endpoint plus $0.01/GB traffic! Expect costs of about $32.85/month per NAT gateway plus $0.045/GB traffic!
- VPC
- CIDR
10.0.0.0/16configurable via the VpcCidrBlock configuration parameter and VpcSubnetCidrBits configuration parameter. - Flow Logs turned on.
- Internet Gateway
- NAT Gateway
- CIDR
- Two public subnets
- NACLs allow inbound port 443 (AWS API, virus database, Amazon Linux 2023 repository) inside VPC, as well as high ports required by NAT Gateway.
- NACLs allow outbound port 443, as well as high ports inside VPC required by NAT Gateway.
- Two private subnets
- NACLs allow inbound port 22 (SSH) restricted to CIDR defined in the SSHIngressCidrIp configuration parameter, 443 inside VPC, as well as high ports required by NAT Gateway.
- NACLs allow outbound port 443, as well as high ports inside VPC plus CIDR defined in the SSHIngressCidrIp configuration parameter.
- Gateway VPC Endpoints for DynamoDB and S3.
- Interface VPC Endpoints for SNS, EventBridge, and SQS.
- Security group
- Allow inbound port 22 restricted to CIDR defined in the SSHIngressCidrIp configuration parameter.
- Allow outbound port 443.
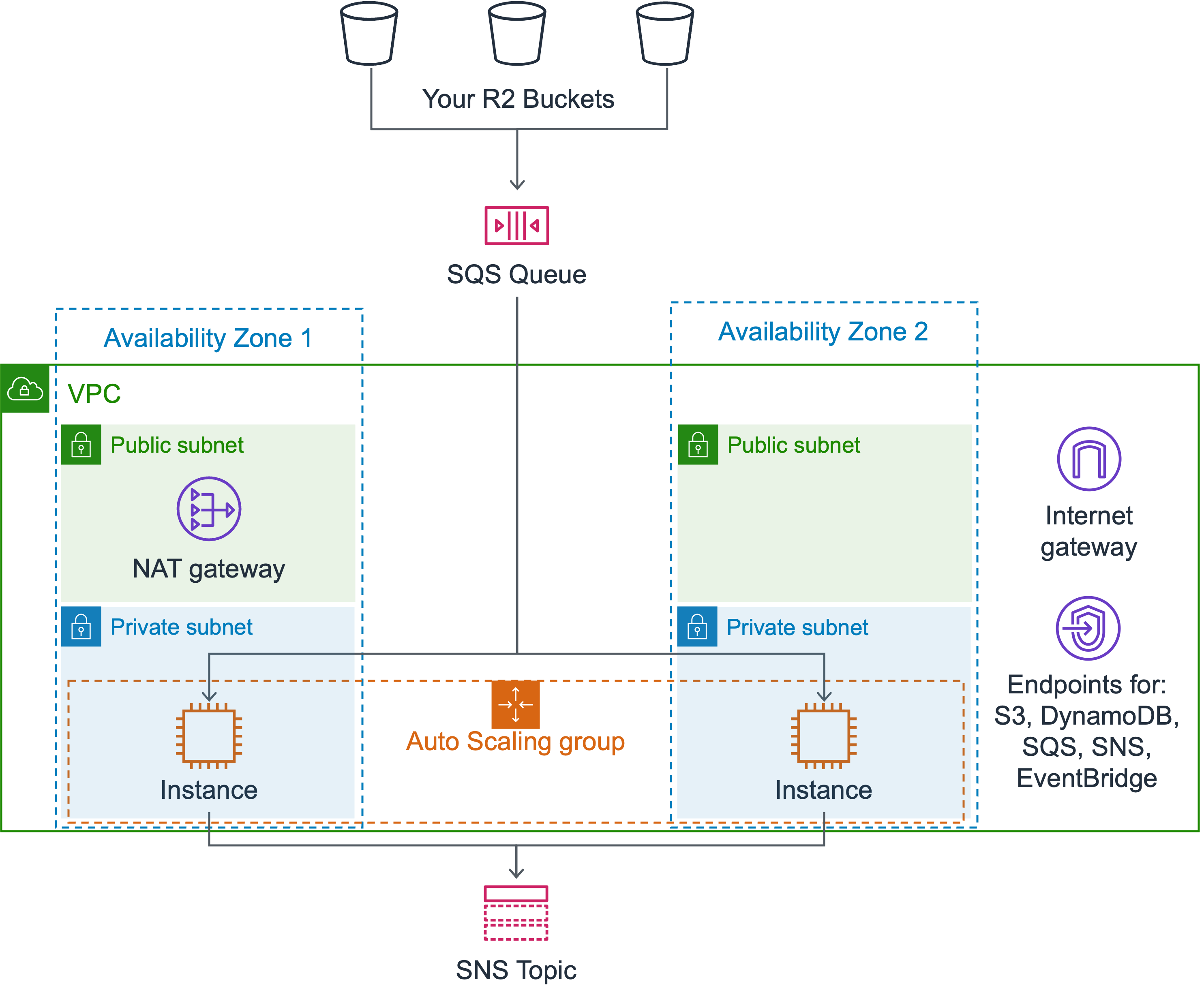
Expect costs of about $14.60/month per VPC interface endpoint plus $0.01/GB traffic! Expect costs of about $32.85/month per NAT gateway plus $0.045/GB traffic!
- VPC
- CIDR
10.0.0.0/16configurable via the VpcCidrBlock configuration parameter and VpcSubnetCidrBits configuration parameter. - Flow Logs turned on.
- Internet Gateway
- NAT Gateway
- CIDR
- Two public subnets
- NACLs allow inbound port 443 (AWS API, virus database, Amazon Linux 2023 repository) inside VPC, as well as high ports required by NAT Gateway.
- NACLs allow outbound port 443, as well as high ports inside VPC required by NAT Gateway.
- Two private subnets
- NACLs allow inbound port 22 (SSH) restricted to CIDR defined in the SSHIngressCidrIp configuration parameter, 443 inside VPC, as well as high ports required by NAT Gateway.
- NACLs allow outbound port 443, as well as high ports inside VPC plus CIDR defined in the SSHIngressCidrIp configuration parameter.
- Gateway VPC Endpoints for DynamoDB and S3.
- Interface VPC Endpoints for SNS, EventBridge, and SQS.
- Security group
- Allow inbound port 22 restricted to CIDR defined in the SSHIngressCidrIp configuration parameter.
- Allow outbound port 443.
Existing VPC
VPC is managed by the customer. The VPC must fulfill specific requirements defined in the Existing VPC Network Guide.