Amazon Connect attachment scanning
This feature is only available for bucketAV for Amazon S3!
You can configure Amazon Connect to scan attachments that are sent during a chat or uploaded to a case. You can scan attachments for malware before they are approved to be shared between participants of a chat with bucketAV.
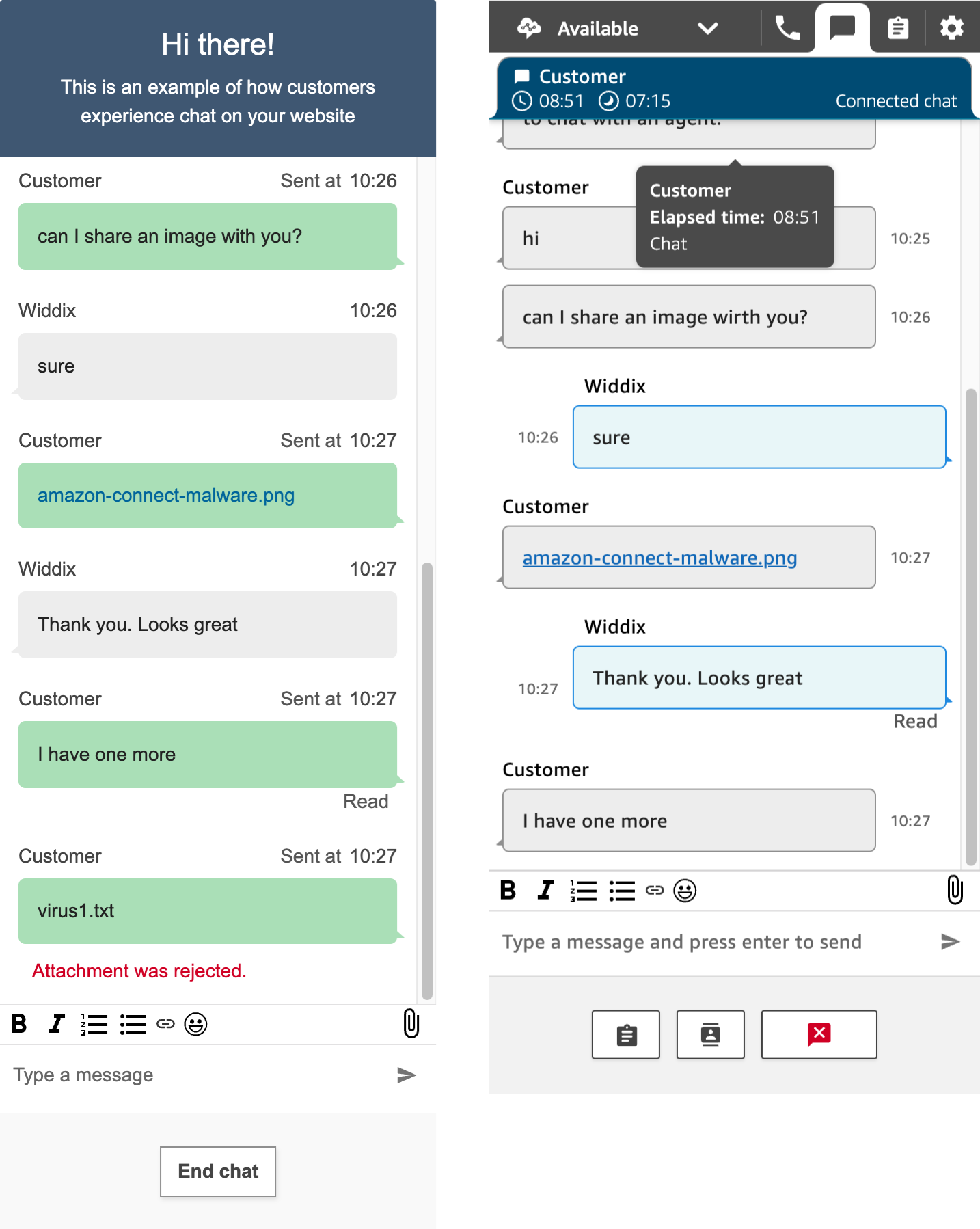
The following figure shows an interaction between a user and an agent. The user (on the left) uploads a clean file first, followed by a virus. The agent (on the right) only receives the clean file.
Setup
Requires bucketAV for Amazon S3 powered by ClamAV® version >= 2.9.0, or bucketAV for Amazon S3 powered by Sophos® version >= 2.0.0.
To update to the latest version, follow the Update Guide.
(requires a running bucketAV installation)The ReportCleanFiles configuration parameter must be set to
true.
- Set the Stack name to
bucketav-connect. - Set the BucketAVStackName parameter to the stack name of bucketAV (if you followed the docs, the name is
bucketav). - Select I acknowledge that AWS CloudFormation might create IAM resources.
- Click on the Create stack button to save.
- Wait for the stack to reach status
CREATE_COMPLETE. - Click on the Outputs tab to get the ScannerLambdaFunctionName.
- Follow the Amazon Connect documentation to add an attachment scanner to your Amazon Connect instance and select the Lambda function returned in the previous step.
CloudFormation snippet
# [...]
Resources:
# [...]
Connect:
Type: 'AWS::CloudFormation::Stack'
Properties:
Parameters:
BucketAVStackName: 'bucketav' # if you followed the docs, the name is bucketav
TemplateURL: 'https://bucketav-add-ons.s3.eu-west-1.amazonaws.com/connect/v2.6.0/bucketav-add-on-connect.yaml'
Terraform snippet
resource "aws_cloudformation_stack" "bucketav_add_on_connect" {
name = "bucketav-connect"
template_url = "https://bucketav-add-ons.s3.eu-west-1.amazonaws.com/connect/v2.6.0/bucketav-add-on-connect.yaml"
capabilities = ["CAPABILITY_IAM"]
parameters = {
BucketAVStackName = "bucketav" # if you followed the docs, the name is bucketav
}
}
Update
- To update this Add-On to version v2.6.0, go to the AWS CloudFormation Management Console.
- Double-check the region at the top right.
- Search for
bucketav-connect, otherwise search for the name you specified. - Select the stack and press the Update stack button; press Make a direct update.
- Select Replace existing template and set the Amazon S3 URL to
https://bucketav-add-ons.s3.eu-west-1.amazonaws.com/connect/v2.6.0/bucketav-add-on-connect.yamlCopy - Click on Next.
- Scroll to the bottom of the page and click on Next.
- Scroll to the bottom of the page, enable I acknowledge that AWS CloudFormation might create IAM resources, and click on Next.
- Scroll to the bottom of the page and click on Submit.
- While the update runs, the stack status is UPDATE_IN_PROGRES. Reload the table from time to time and …
- … wait until the CloudFormation stack status switches to UPDATE_COMPLETE.
Architecture
The following AWS services are used:
- DynamoDB Table to store scan results temporarily.
- SNS Subscription to connect to the Findings Topic.
- Lambda Function to store the scan results in DynampDB and to implement the Amazon Connect attachment scanner.
- CloudWatch Alarms to monitor the used AWS services.
- CloudWatch Logs to store logs.
Run Lambda in a VPC
By default, the add-on deploys Lambda functions with access to the Internet. In case you want to deploy the Lambda functions into a VPC, configure the LambdaVpc and LambdaSubnets parameters.
The add-on requires access to the following endpoints (replace REGION with the AWS region like eu-west-1):
https://dynamodb.REGION.amazonaws.com
Ensure that the subnets configured in the LambdaSubnets parameter have access to these endpoints via a NAT Gateway or VPC Endpoints.
Release Notes
Subscribe to our Atom feed or newsletter to stay up-to-date! We also publish a machine-readable JSON file.
v2.6.0
Changes:
- Improve SQS fairness when system is under load
Release date:2025-07-28
Template: https://bucketav-add-ons.s3.eu-west-1.amazonaws.com/connect/v2.6.0/bucketav-add-on-connect.yaml
v2.5.0
Changes:
- Optionally run Lambda functions in a VPC
Release date:2025-04-15
Template: https://bucketav-add-ons.s3.eu-west-1.amazonaws.com/connect/v2.5.0/bucketav-add-on-connect.yaml
v2.4.0
Changes:
- Update Lambda Node.js runtime to version 22
Release date:2025-02-28
Template: https://bucketav-add-ons.s3.eu-west-1.amazonaws.com/connect/v2.4.0/bucketav-add-on-connect.yaml
v2.3.0
Changes:
- Reserved Concurrent Execution for Lambda functions
Release date:2024-11-19
Template: https://bucketav-add-ons.s3.eu-west-1.amazonaws.com/connect/v2.3.0/bucketav-add-on-connect.yaml
v2.2.1
Changes:
- Bug fixes
Release date:2024-07-09
Template: https://bucketav-add-ons.s3.eu-west-1.amazonaws.com/connect/v2.2.1/bucketav-add-on-connect.yaml
v2.2.0
Changes:
- Update Lambda runtime to Node.js 20
Release date:2024-02-14
Template: https://bucketav-add-ons.s3.eu-west-1.amazonaws.com/connect/v2.2.0/bucketav-add-on-connect.yaml
v2.1.0
Changes:
- Add Service Discovery
Release date:2023-12-07
Template: https://bucketav-add-ons.s3.eu-west-1.amazonaws.com/connect/v2.1.0/bucketav-add-on-connect.yaml
v2.0.1
Changes:
- Bug fixes
Release date:2023-11-16
Template: https://bucketav-add-ons.s3.eu-west-1.amazonaws.com/connect/v2.0.1/bucketav-add-on-connect.yaml
v2.0.0
Changes:
- Initial release
Release date:2023-11-15
Template: https://bucketav-add-ons.s3.eu-west-1.amazonaws.com/connect/v2.0.0/bucketav-add-on-connect.yaml